PGPP: A hack on the broken and privacy invading network?
PGPP is a new mobile carrier that aims to provide increased user privacy and security. It is designed to use already existing infrastructure with clever techniques that reduce the usefulness of the 3 main tracking tools used by carriers. This project is intended to hamper bulk data collection, but does not claim it would withstand a targetted attack from a state actor. This is because a state actor could and probably would have full visibility of the network.
HOW THE APP WORKS IN PRACTISE#
You will need a phone that has support for a eSIM, which is most phones after 2018, Though do check. For testing, I used both the Fairphone 4 and a Pixel 4a (non-5G as I wanted to test the usefulness of this service on non-5G device). Getting the service requires Google Play (though Aurora store works) and you will need to install it in a non-work profile. From there all you will need to do is go through the setup process with consists clicking through a few info pages; setting a plane and entering your details. When you have gone through that you will be presented with this page:
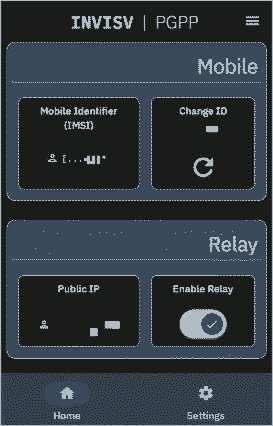
From here you can enable the relay, though if you use hot spots you might want to opt for a conventional VPN as it won’t work with the relay at present (a fix is apparently coming and is a known to be broken atm), you can change your IMSI and re-new your plan along with enabling relay. The app doesn’t really have much going on to be honest, though in fairness it doesn’t need much.
Compatability#
As this service is still very much in beta, there are a few things to take into consideration. You will need a device that has eSIM support and 4G/LTE support(though I think eSIMs were only a thing on 4G devices). The testing for this service has mainly been done on pixel devices and some Samsung devices, the site says that the phones that work best are Pixel 4 and Samsung S22 and newer models [1]. Though, most of the testing has been done on stock android. When you have the app installed and the service registered, often the first eSIM installed will show some normal carrier in the carrier information, you will need to renew the IMSI/service. The second sim should register as PGPP in the carrier information. If this isn’t the case you can try again or contact their support, they are helpful, but I don’t think it is a big support team by any means. If you find a device that does work with it, it might be worth emailing the company with the model, ROM (if any), build information and so on.
I assume it gose without saying that you will need a unlocked phone for this service to work? It uses multiple carriers from O2, EE to 3 (well at least as far as I can see).
EDIT: Some Android 12 devices, all Android 13,do not allow “untrusted carriers” to set the carrier name, so some piggy back networks (networks that use other companies infrastructure), resulting in the network showing the wrong carrier. The developers are pushing out a new build of the application that should handle this, though I am unsure what the fix will be. I will update here when I know more and can test the new build.
Something to keep in mind when using the service#
If you are wanting to keep your privacy when it comes to location privacy, you will probably want to be using some de-googled rom. This is because Google (and other services like Facebook) take your location, often at all times. Though that being said there are some settings to disable that if you are running a stock rom, though I won’t cover that in this artical. Also, if you are just wanting to keep your location data private when it comes to your carrier this would help with that (I am not sure what threat model that would be included in but if it is your model, enjoy).
Also, when registering the service you will need to use WI-FI as other SIMs might break it, also when renewing the eSIM as the previous one is deleted before registering the service.
A abridged technical section#
If you are technically minded and want a good understanding of this technology, please go and read the white paper released on this. It is in the sources [2]. Also if you want a video form of this, I recommend you watch a talk done about this exact topic [3]. What I have written here is my understanding of the service but I am not an expert and do not fully understand the inner workings of both cellular infrastructure nor of PGPP’s service.
IMIE & IMSI#
The IMIE and IMSI are used to directly identify you by both individual bad actors and telecoms providers. Telecoms providers use this information to gather a precisest picture of where you go around in your daily life and often sell this information on to 3rd parties which can link it to your online movements. Individual actors use this information to see where you go in your life and there is a whole world of trouble you can get into, which I am sure you can imagine.
These days telecoms providers understand the importance of keeping this information private, well at least from people they don’t want to have. They created a 3rd identifier but one that is completely random called a GUTI (Globally Unique Temporary Identifier) and while the carrier knows who you are there isn’t a simple way to turn that string into a user. Though there are ways to expose even the IMIE sometimes.
Billing#
Billing is a complicated problem to solve. They required that they could validate that the user was a customer but not who the specific user was, along with some level of uniqueness (uniqueness as in how they monitor payments rather than uniqueness of user) as they settled on the idea of using tokens that are given to the user at the beginning of the billing process. If they used some standard authentication it would completely defeats all of privacy benefits the service offers along with most other solutions like cryptocurrencies and other styles of crypto. They ended up using their own in house solution based on both “one-more-rsa-inversion problems and the security of chaum’s bine signiture shceme. Journal of Cryptogy 2003” and “Blind signitures for untraceable payments. In Crypto, 1983”. It is called a PGPP token, at the beginning of the billing procedure the user is given tokens that can be verified by PGPP but not identify the user. These tokens are valid for a period of time (I think a year).
Tracking Areas#
SIDE NOTE: This is the area I understand the least here so some parts might be wrong or not the full truth. Once again, if you need accuracy please read through the white paper or watch their video.
Tracking areas, in conventional systems, are used to provide instant data to the phone; like a phone or SMS call. Though they have the added downside of being able to see where the user is to a frightening level of accuracy. They are affectively a group of cellular towers near (maybe a radios of a few km). This allows your phone to jump between the ones that have the strongest signal. You are provided a list of sixteen tracking areas that you can move between effectively making the tracking area a union of all of those areas. When you move out of this area your phone will request a new list of towers to use. They will also provide you some other tracking area lists but they are normally in close proximity to one another because they are designed for speed.
PGPP dose a similar thing but instead of providing a pre-computed tracking area they generate one on-the-fly and uniquely for each user. When they connect for the first time or when they request a new tracking area the Mobility Management Entity (MME), which is a machine that manages the connection between the device and eNodeB (some other device that deals with the connection), it provides the tracking area the device is already connected to. The MME then generates a new tracking area list. It will generate a list of up to 16 random additional and adjacent tracking areas that the user is in.
Legality#
Most governments like the UK, US and EU require data to be collected for SMS, calls, location and internet traffic. The techniques that this service uses means: A. SMS and calls are supported by this network so the data isn’t collected; B. location data is irreverential as it both is unspecific and isn’t tied to the user with something like financial data; C. Internet traffic is pushed through a multi-hop relay, much in the same way Apple’s relay works[4], meaning the traffic given to law enforcement would not get more than encrypted traffic going to a relay. In these countries there are not KYC (know your customer) laws yet for mobile plans and the like so the information they gather about you on payment isn’t required to be tied to the service they provide.
In a similar vain, Signal, WhatsApp and Proton are all required to do the same but they can also only provide minimal information about the user because of how their systems are archatected.
Opinion#
I have only used this service for a few months now but the service has shown it’s self to be a very consistent product. While registering can go wrong sometimes, I have not had a issue with anything after. I think for the general person it is a very affective way of thwarting privacy violations from cellular companies. It uses many stages of removing the user/payer from the service that they carry around with them and the more people that adopt the service (and normal people) will end up considerably improving the legitimacy of using this; much in the same way that normal people using TOR will.
For some very high threat model people it will in no way help them, mainly because an adversary with high access would be able to collect all the traffic and pin point thegf user. That is not to say it is useless though, for bulk data collection this method is very a effective solution.
SOURCES:#
[2] https://arxiv.org/abs/2009.09035